HITRUST certification is many things. It’s a shortcut to securing your system against the danger of data breaches, a process for ensuring compliance with HIPAA and other regulations, and a competitive edge for your business in the increasingly crowded healthcare information space, and a business accelerator, as it can cut your sales cycles by 50% or more.
One thing it is definitely not, however, is an easy accomplishment.
The Road To HITRUST
Currently, the HITRUST CSF (certified security framework) monitors over 1,200 potential controls, also known as requirement statements, across multiple regulatory bodies. At the beginning of your HITRUST process your assessor will determine how many of these 1,200 controls your organization must attest to based on a risk assessment. A low risk organization, for example, would require attestation to 200 or 300 controls, while a high risk organization may require attestation to 800 or more.
The Challenges Of HITRUST
Two basic barriers create delays to achieving HITRUST certification.
One barrier is the sheer complexity of HITRUST, which is difficult for newcomers to navigate. Not only are there 1,800 potential controls in the framework, but these guidelines are constantly changing. Businesses must continually respond to them and update their processes – or put in place automated tools that do so for them.
Having so many controls to satisfy creates another barrier – the need for extensive resources and expert guidance. Achieving HITRUST certification without an experienced cloud partner is virtually impossible. And in terms of both time and resources, satisfying HITRUST guidelines means considerable pressure on your bottom line. Naturally, the cost of HITRUST is expensive.
The HITRUST Solution
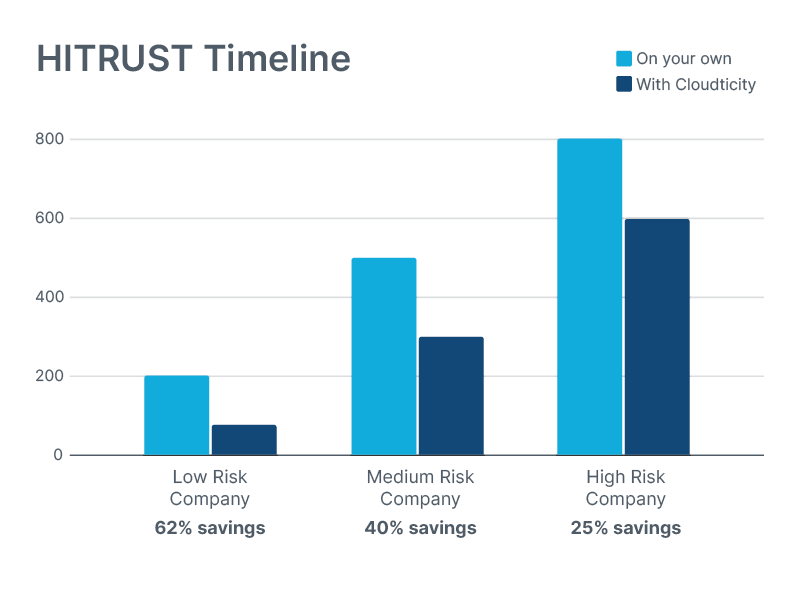
As one of only a handful of HITRUST inheritance partners in the world, we created the Cloudticity HITRUST Inheritance Program. The program is designed to accelerate your HITRUST certification timeline by 25-62%. In order to understand how the program works we must first understand inheritable controls and how they help.
Understanding Inheritable Controls
Working with public cloud service providers like Amazon Web Services (AWS), Microsoft Azure, and Google Cloud can make achieving compliance faster and simpler. Because security and compliance in the cloud is a shared responsibility, cloud service providers (CSPs) who are certified HITRUST inheritance partners share a significant part of the load in regards to the HITRUST process. When you use their HITRUST Certified services, you can inherit attestation to controls that they've already met.
There are two kinds of inheritance: full inheritance and partial inheritance. Both can help you achieve your HITRUST goals faster, and reduce the work needed to achieve HITRUST.
Here's an example of a fully inheritable control: one HITRUST control requires least privilege access to the data center where protected health information (PHI) is stored. When your organization doesn't own the physical infrastructure, it can't be responsible for this control. Instead, your organization inherits attestation to this control via your CSP. That means that this is a box on your HITRUST assessment that you can simply check off without putting in any effort or investing time!
There are also shared controls which are partially inheritable. For example, one control states that you must have anti-malware or anti-spyware deployed on end-user devices. The CSP is responsible for installing endpoint security on the services it delivers while your organization is responsible for this control in regards to its own endpoints, so you partially inherit this control from the CSP.
How Cloudticity HITRUST Inheritance Program Works
When you purchase your AWS, Azure, or Google Cloud services through Cloudticity you get access to even more inheritable and partially inheritable HITRUST controls – 357 to be exact. This is because Cloudticity has automated 357 HITRUST controls that are shared with the client through the MSP relationship, and this number continues to grow. In fact, many of our clients seek out our managed services in order to reap the benefits of our HITRUST Inheritance Program, which shortens the HITRUST journey by 25-62%, depending on your company's risk profile.
Along with HITRUST inheritance, partnering with Cloudticity provides managed services, managed security, and managed compliance services alongside an always-on help desk and incident response team. This allows our customers to allocate their IT bandwidth towards activities that drive business growth and value for customers, like innovation and product development, rather than merely keeping the lights on.
A Partner For The Whole Journey
With the Cloudticity HITRUST Inheritance Program, you're never on your own to navigate the complex and often convoluted terrain of HITRUST. We partner with you for the whole journey in order to provide the knowledge and tools necessary to ensure you don't make mistakes, get stuck, or need to backtrack.
Accelerate Your Path To HITRUST
To learn more about how the Cloudticity HITRUST Inheritance Program download the free white paper. Or schedule a free consultation to learn how you can work with us to make your HITRUST dreams a reality.


